1. Arrange students into groups. Each group needs at least ONE person who has a mobile device.
2. If their phone camera doesn't automatically detect and decode QR codes, ask students to
4. Cut them out and place them around your class / school.
1. Give each group a clipboard and a piece of paper so they can write down the decoded questions and their answers to them.
2. Explain to the students that the codes are hidden around the school. Each team will get ONE point for each question they correctly decode and copy down onto their sheet, and a further TWO points if they can then provide the correct answer and write this down underneath the question.
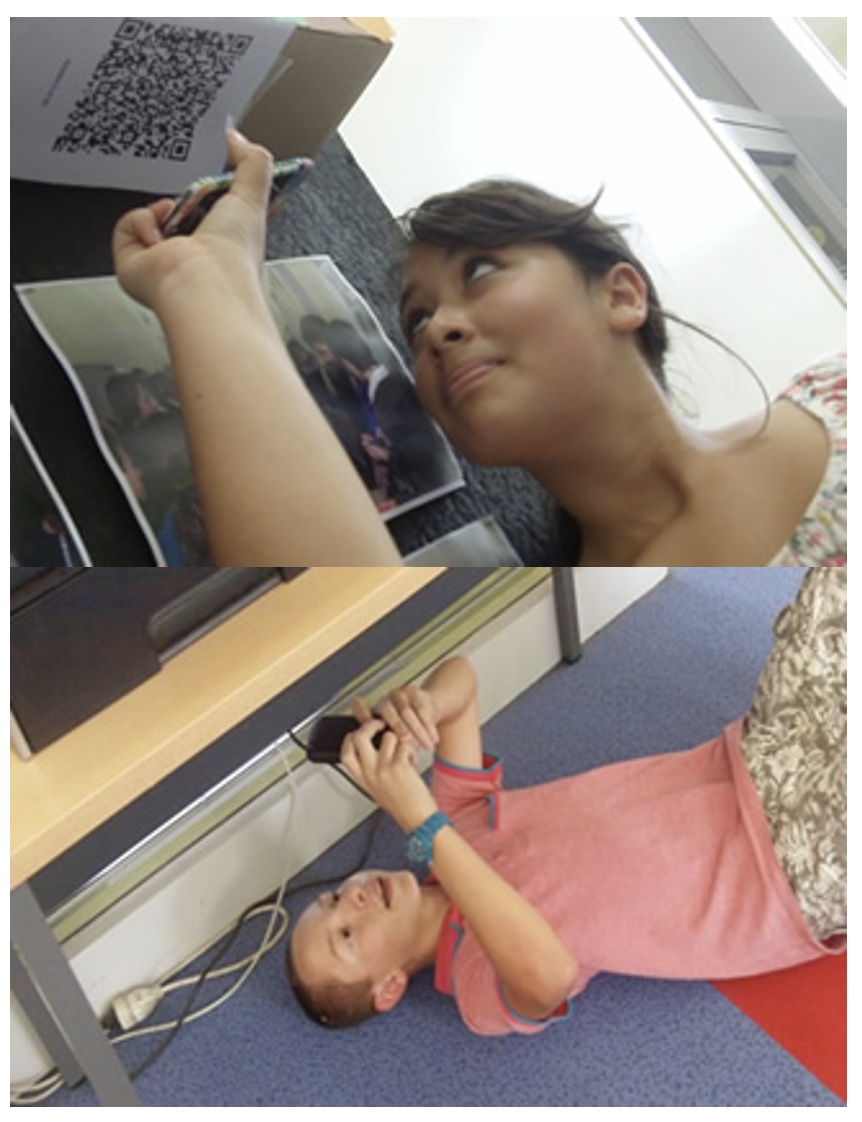
3. Away they go! The winner is the first team to return with the most correct answers in the time available. This could be within a lesson, or during a lunchbreak, or even over several days!
4. A detailed case study in how to set up a successful QR Scavenger Hunt using this tool can be found here.
Question | Answer |
| 1. CONFIDANT reputation system takes into consideration only the | negative reputation | 2. in schemes that reward ......, a node can behave well for a period of time to boost its reputation before launching an attack | good behavior | 3. false accusations is a disadvantage of ...... reputation system | CONFIDANT | 4. to prevent denial of service attack in core reputation system ...... is not shared with other nodes | negative reputation | 5. one of challenges associated with the design of...... in a MANET they are prone to attacks from malicious nodes | reputation systems | 6. when Purse Model were proposed assume that each node has a .... | tamper-resistant hardware module | 7. in ..... The source of the packet needs to know how many hops the packet needs to travel so that it loads the packet with enough cash to satisfy all the forwarding nodes | Purse Model | 8. in purce model The source does not need to expend any cash to originate a packet leaving the scheme open to ....... from the source | denial of service attacks | 9. ....... can be easily detected if all routing messages are signed | spoofing | 10. disadvantage of ....... messages it increases the overhead since it increases the size of routing messages and the amount of processing needed to process each routing message | signing routing | 11. Trade-off between setting a threshold to such a small level that several ..... are generated | false positives | 12. A node may advertise a large number of nodes as its neighbors may create a ..... | black hole |

Question 1 (of 12)

Question 2 (of 12)

Question 3 (of 12)

Question 4 (of 12)

Question 5 (of 12)

Question 6 (of 12)

Question 7 (of 12)

Question 8 (of 12)

Question 9 (of 12)

Question 10 (of 12)

Question 11 (of 12)

Question 12 (of 12)