
PREMIUM LOGIN
ClassTools Premium membership gives access to all templates, no advertisements, personal branding and many other benefits!
| Username: | ||
| Password: | ||
|
Submit
Cancel
|
||
| Not a member? | ||

PREMIUM LOGIN
ClassTools Premium membership gives access to all templates, no advertisements, personal branding and many other benefits!
| Username: | ||
| Password: | ||
|
Submit
Cancel
|
||
| Not a member? | ||
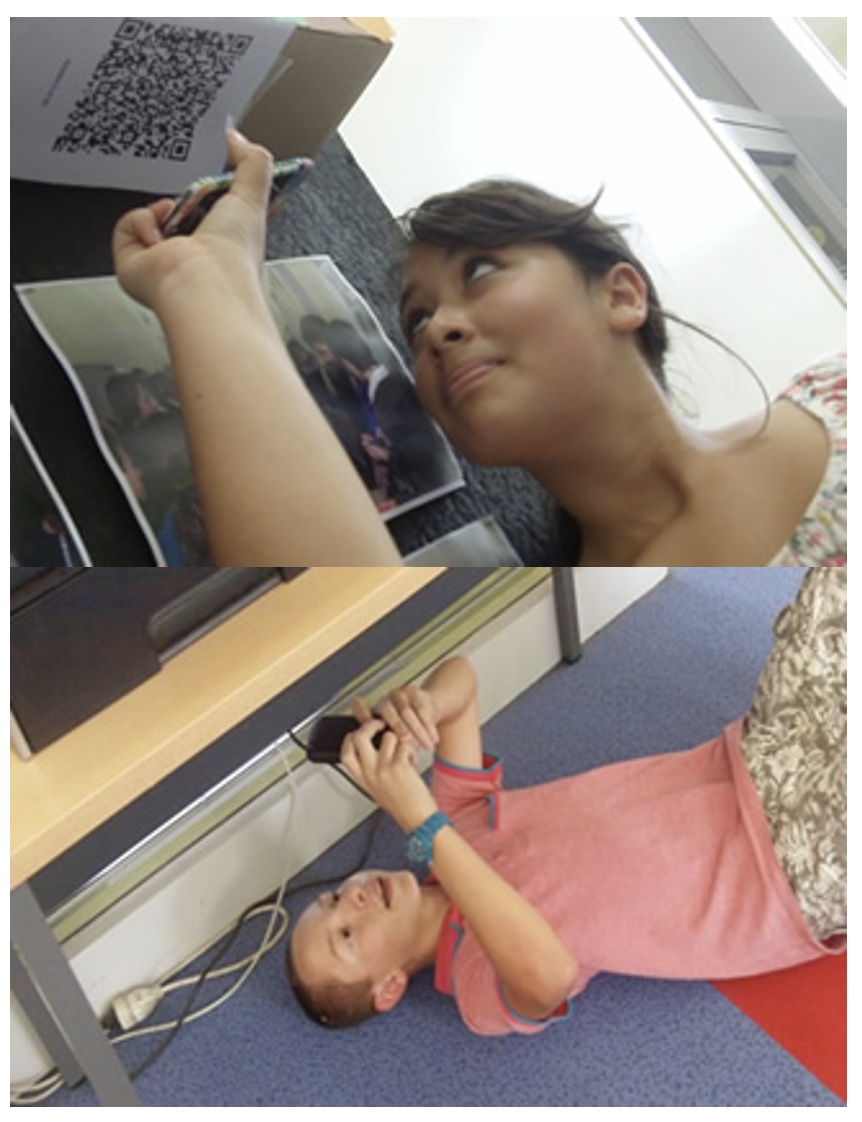
1. Arrange students into groups. Each group needs at least ONE person who has a mobile device.
2. If their phone camera doesn't automatically detect and decode QR codes, ask students to
4. Cut them out and place them around your class / school.
1. Give each group a clipboard and a piece of paper so they can write down the decoded questions and their answers to them.
2. Explain to the students that the codes are hidden around the school. Each team will get ONE point for each question they correctly decode and copy down onto their sheet, and a further TWO points if they can then provide the correct answer and write this down underneath the question.
3. Away they go! The winner is the first team to return with the most correct answers in the time available. This could be within a lesson, or during a lunchbreak, or even over several days!
4. A detailed case study in how to set up a successful QR Scavenger Hunt using this tool can be found here.
Question | Answer |
| 1. a licensing concept created that builds upon traditional copyright practices to define possibilities that exist between the standard "all rights reserved" full copyright and public domain "no rights reserved" | Creative Commons | 2. using or characterized by computer technology | Digital | 3. rules about the proper and polite way to communicate with other people when you are using the Internet | Netiquette | 4. a Web site that contains online personal reflections, comments, and often hyperlinks provided by the writer | Blog | 5. a Web site that allows visitors to make changes, contributions, or corrections | Wiki | 6. a word or phrase preceded by the symbol # that classifies or categorizes the accompanying text | (Hash)tag | 7. forms of electronic through which users create online communities to share information, ideas, personal messages, and other content | Social Media | 8. a scam by which an e-mail user is duped into revealing personal or confidential information which the scammer can use illicitly | Phishing | 9. To distribute to a larger audience or group of receivers by way of a network | Feeds | 10. Audio digital recording as a program | Podcast | 11. to identify and store a website so that one can return to it easily | Bookmark | 12. The legal right granted to an author, composer, playwright, publisher, or distributor to exclusive publication, production,sale, or distribution of a literary, musical, dramatic, or artistic work | Copyright | 13. the character of an individual viewed as a member of society | Citizenship | 14. Video digital recording as a program | Vodcast | 15. a blog that contains video material | Vlog | 16. online harassment, which can be in the form of flames, comments made in chat rooms, the sending of offensive or cruel e-mail, or even harassing others by posting on blogs, Web pages or social networking sites | Cyberbullying | 17. crime whereby criminals impersonate individuals, usually for financial gain. If a thief is able to access your personal information, s/he can use it to commit fraud in your name | Identity Theft | 18. To publish a message in an online forum or newsgroup | Posting | 19. consists of the skills of collaboration, digital literacy, critical thinking, and problem-solving | 21st Century Learning | 20. A virtual, visual representation of a person or player | Avatar | 21. Text or a graphic that takes you to another page | Links | 22. A legal doctrine that portions of copyrighted materials may be used without permission of the copyright owner provided the use is fair and reasonable, does not substantially impair the value of the materials, and does not curtail the profits reasonably expected by the owner | Fair Use | 23. An official document, card, etc., that gives you permission to do, use, or have something | License | 24. The ascribing of a work to a particular author or artist | Attribution | 25. the quality of habits, actions, and consumption patterns that impact the ecology of digital content and communities | Citizenship |

Question 1 (of 25)

Question 2 (of 25)

Question 3 (of 25)

Question 4 (of 25)

Question 5 (of 25)

Question 6 (of 25)

Question 7 (of 25)

Question 8 (of 25)

Question 9 (of 25)

Question 10 (of 25)

Question 11 (of 25)

Question 12 (of 25)

Question 13 (of 25)

Question 14 (of 25)

Question 15 (of 25)

Question 16 (of 25)

Question 17 (of 25)

Question 18 (of 25)

Question 19 (of 25)

Question 20 (of 25)

Question 21 (of 25)

Question 22 (of 25)

Question 23 (of 25)

Question 24 (of 25)

Question 25 (of 25)